
Handala Hack Team and the Stryker Breach
Cyber operations increasingly blur the lines between hacktivism, cybercrime, and state-sponsored warfare. A recent attack attributed to the Handala Hack Team highlights how modern threat actors combine political narratives with highly destructive cyber capabilities.
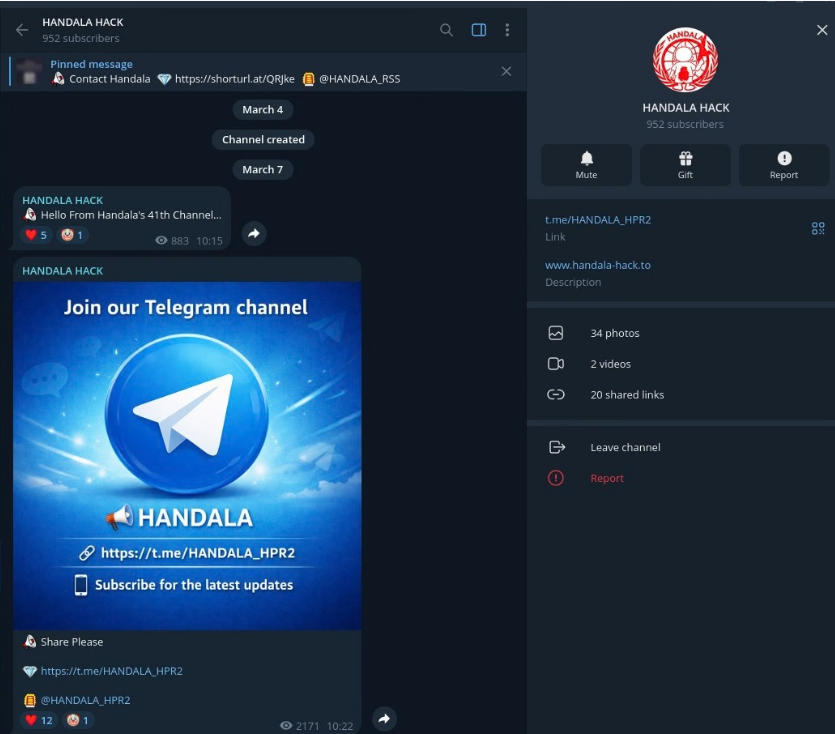
ThreatMon CTI analysis indicates that Handala operates as the public-facing arm of a larger Iranian threat cluster known as Void Manticore, linked to the Ministry of Intelligence and Security (MOIS). The group presents itself as a hacktivist collective, but its operational scale and sophistication suggest a coordinated state-backed campaign.
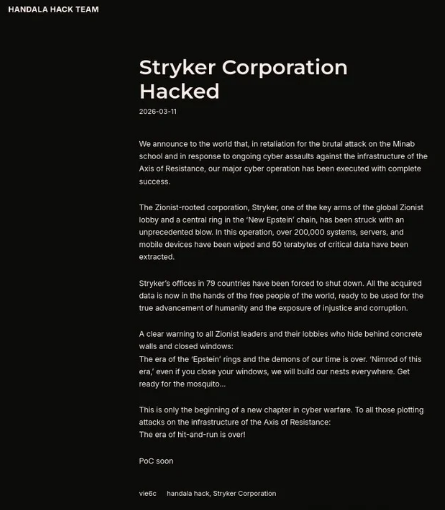
The most significant example of this activity occurred in March 2026, when the group targeted the global medical technology company Stryker Corporation.
On March 11, 2026, Handala claimed responsibility for a destructive cyber operation against Stryker, a Fortune 500 medical technology company.
According to available intelligence and public disclosures, the attack disrupted operations across 79 countries and affected more than 200,000 devices worldwide.
Rather than relying solely on traditional malware, the attackers used an advanced technique:
they weaponized the company’s Microsoft Intune Mobile Device Management (MDM) infrastructure.
By abusing legitimate management tools inside the environment, the attackers were able to push destructive commands across large numbers of devices simultaneously.
This approach represents a Living-off-the-Land (LOTL) technique that bypasses many traditional endpoint security controls.
The event represents one of the largest destructive cyber incidents targeting the medical technology sector to date.

While the group promotes itself as a pro-Palestinian hacktivist movement, technical attribution indicates a more structured organization.
Threat intelligence sources track this actor under several names, including:
Evidence suggests the group operates under the MOIS Counter-Terrorism Division, using hacktivist branding as a cover for state-aligned cyber operations.
Researchers often refer to this structure as “faketivism” a model in which government-directed operations are conducted under the appearance of grassroots cyber activism.
Handala and related clusters have been linked to several destructive cyber operations since 2022.
Albania Government Attacks (2022–2023)
Wiper malware destroyed critical government infrastructure and border management systems.
Israel Targeting Campaigns (2023–2025)
Multiple Israeli organizations, including healthcare and energy institutions, were targeted through wiper malware and data theft campaigns.
Defense Sector Intrusions (2024)
A breach targeting an Israeli radar manufacturer resulted in a threatened 2 TB data leak.
Stryker Corporation Attack (2026)
The first globally distributed Iranian wiper operation affecting tens of thousands of systems across multiple continents.

ThreatMon CTI analysis shows that the group follows a consistent attack pattern. Initial access is often gained through compromised VPN credentials, credential-stuffing attacks, exposed remote access services, or trusted partner and supply-chain connections.
Once inside the network, attackers typically rely on legitimate administrative tools such as Microsoft Intune, PowerShell, and Group Policy changes to execute commands and move laterally, often using RDP to expand their access across systems.
In the final stage of the operation, the group deploys destructive wiper malware including BiBi Wiper, Hatef Wiper, No-Justice (LowEraser), and Handala Wiper. These tools wipe disks, corrupt files, and damage system boot structures, leaving affected machines unusable.
One of the key lessons from the Stryker case is the growing risk associated with cloud-based management infrastructure. Mobile Device Management (MDM) platforms such as Microsoft Intune enable administrators to deploy software, enforce security policies, and remotely manage thousands of devices from a centralized console.
However, if attackers gain privileged access to these platforms, they can weaponize the same administrative capabilities to distribute malicious actions across the entire enterprise environment.
This shift highlights a critical reality: management infrastructure itself is becoming a high-value attack surface in modern cyber operations.
The Stryker incident demonstrates how modern cyber operations increasingly blur the lines between hacktivism and state-backed activity. As attackers continue to exploit cloud infrastructure, identity systems, and enterprise management platforms, organizations must move beyond traditional perimeter-based security.
Understanding threat actor tactics is no longer enough. Security teams must also connect threat intelligence with risk visibility and governance processes.
This is where intelligence-driven security and GRC capabilities become critical. Organizations must be able to transform external threat signals into actionable risk insights, enabling faster detection of emerging attack patterns and stronger protection across the digital attack surface.