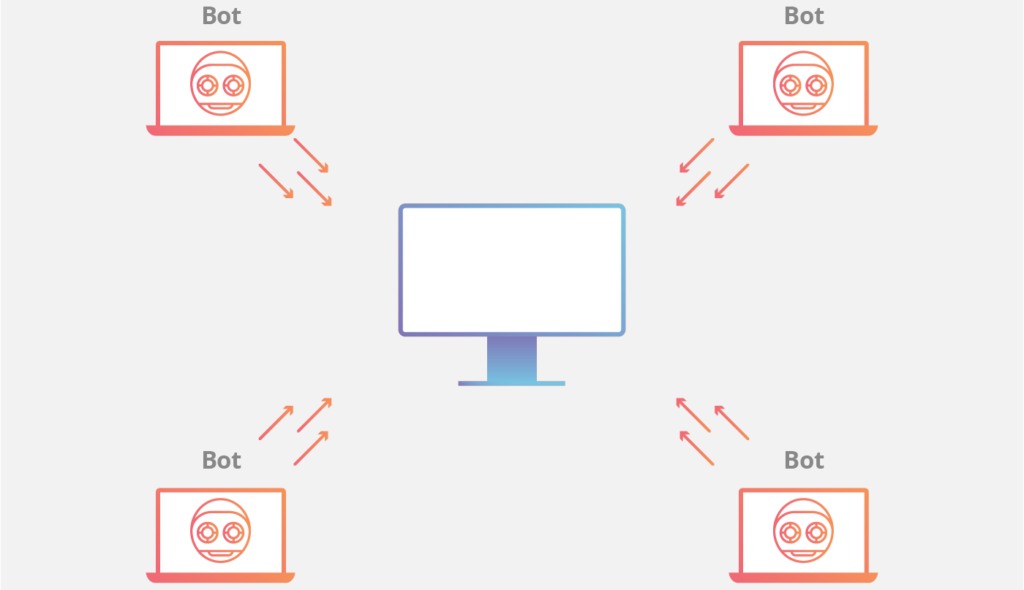
A botnet is a network of compromised computers controlled by a malicious actor, often used to launch large-scale cyber attacks.
Cyber attackers establish a network by infecting computers with malware. This remotely controlled malware is called a “bot“. The network of these bots is called a “botnet“. These computers are also called zombies.
Sometimes cyber attackers set up a large botnet to make it easier and more organized for attacks to be carried out. The attackers often use an infected email attachment, links, website or physical tools to save malware on the computer. Bots are often used by attackers to DDoS attacks, data theft, distribution of malware, spam mails, and to earn money from advertisements.
Attackers can steal a lot of data from computers included in the botnet network. Attackers sell the data they stole from your computer. These data are specifically usernames and passwords.
Threat actors sell or rent these botnets on the Dark Web & Deep Web or Black Markets. Some attacks can be made with botnets created or purchased by attackers.Botnets are often used for this purpose.
Attackers controlling the botnet command the bots to access a website or IP address simultaneously. Website traffic intensifies due to requests from many computers to the specified address. So the site may crash. This is the DDos attack.
This is done through large spam campaigns aimed at stealing user account information such as banking logins or email information.
Most attacks on a single computer are also done with botnets. The goal here is to use multiple computers in an attack.