In this article, Microsoft IIS Server vulnerabilities and ways to mitigate these threats will be discussed.
There are multiple tools available to find out which web server is used.
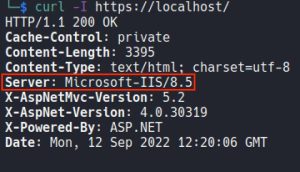
The first of these is curl -I command. curl -I command is run on terminal in order to learn web server.
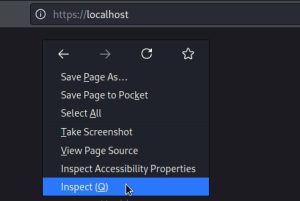
Second, It can be found by viewing the header in the browser.
These steps should be followed:
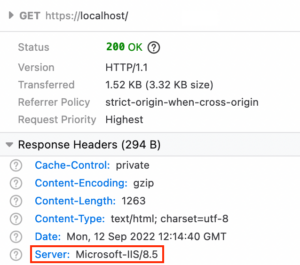
Here is the web server and version used on the website.
A threat actor that learns web server and version info used on the website can use this information for malicious purposes.
Web servers can contain exploitable bugs like any software. These can also be major flaws that could cause an attacker to remotely execute code in the system.
An attacker who exploits this vulnerability can escalate their privileges, causing more critical problems. For example, the vulnerability tracked by code CVE-2022-30209 (CVSS: 7.4) is a privilege escalation issue.
It can also allow a remote attacker to perform a denial-of-service (DoS) attack. This flaw is tracked as CVE-2019-0941(CVSS: 7.5).
In addition, they can create buffer overflows to take control of the Web server and attack the system to replace Web pages or take them down.
It is mentioned above are just a few of the ways web servers can be exploited. There are important actions to be taken to mitigate these threats.
These actions are important to protect the assets in the cyber world against a possible attack.
https://blog.avast.com/create-a-secure-web-server-avast