PyPI Package ‘secretslib’ Drops Fileless Cryptominer to Linux Systems
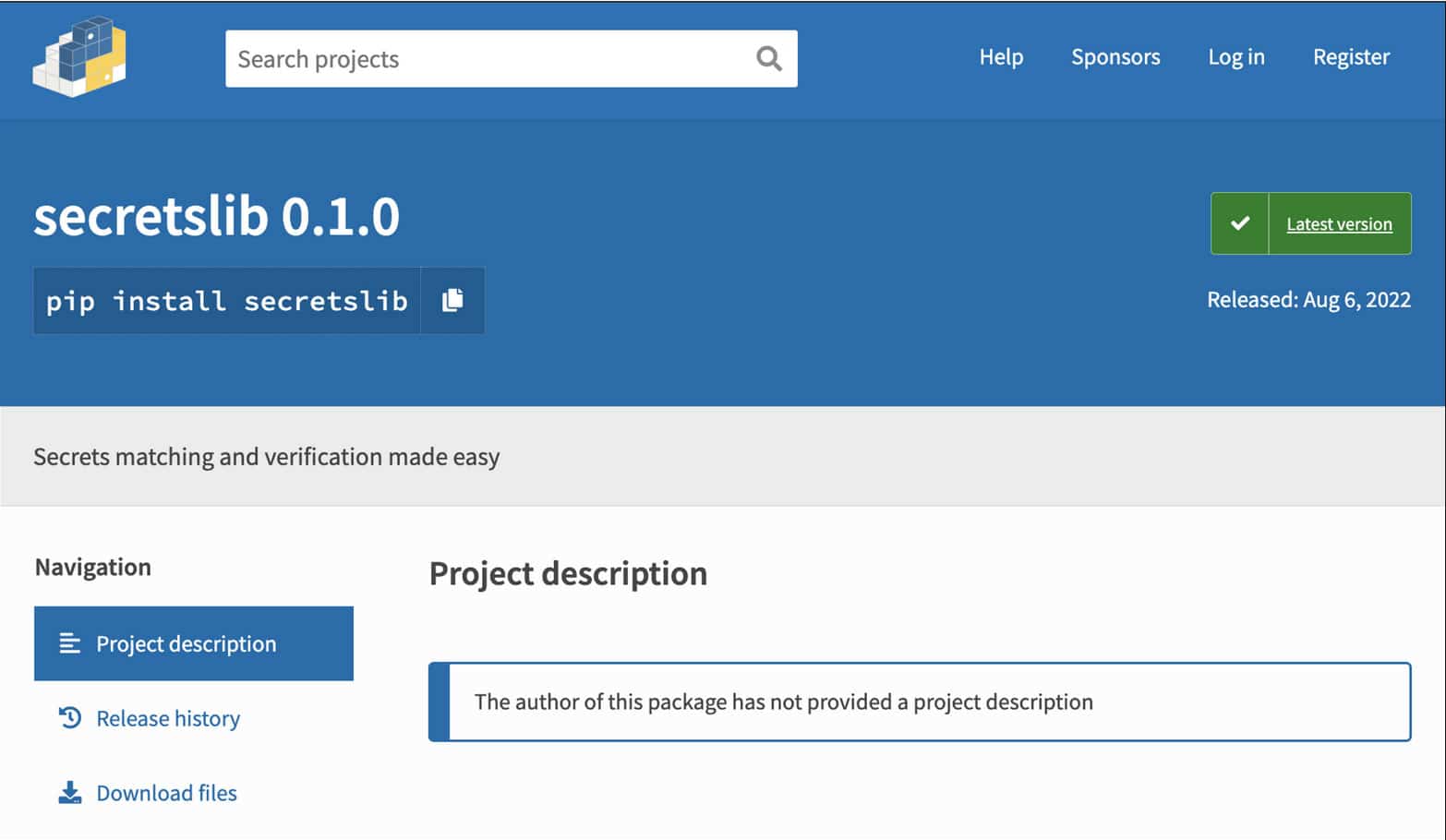
A PyPI package named “secretslib” has been identified by Sonatype, which describes itself as “secret mapping and verification made easy”. The package secretly runs cryptominers in the memory of the Linux machine, a technique largely used by fileless malware and cryptominers. Secretslib was downloaded 93 times before it was deleted.
The threat actor that released the malicious package used the identity and contact details of a genuine national lab software engineer in a US Department of Energy-funded lab to give credibility to their malware.
Sonatype’s automated malware detection systems, available as part of the Nexus Firewall, flagged the ‘secretslib’ PyPI package as potentially malicious.
At the time of release, the package looked like a library that helped match and validate secrets.
The threat actor does this by executing a post-installation Linux executable from a remote server, whose main task is to act as a Monero cryptominer and then directly drop an ELF file (“memfd”) into memory that is deleted by the “secretslib” package.
The goal is to trick users into downloading toxic libraries by assigning them to trusted, popular maintainers without their knowledge or approval.
References:
https://blog.sonatype.com/pypi-package-secretslib-drops-fileless-linux-malware-to-mine-monero







