Unraveling the Complex Infection Chain: Analysis of the SideCopy APT's Attack
Unraveling the Complex Infection Chain: Analysis of the SideCopy APT's Attack
The SideCopy APT Group's infection chain involves multiple steps, each carefully orchestrated to ensure successful compromise. The attack commences with a phishing email, leveraging social engineering techniques to trick victims into interacting with malicious content. The subsequent stages include the distribution of ZIP archives, HTA files, and the establishment of persistency mechanisms. Finally, the attackers deploy a sophisticated RAT in the compromised system, enabling unauthorized remote access and control.
This report presents a list of Indicators of Compromise (IOCs) associated with the SideCopy APT Group's infection chain. These IOCs, including file hashes, IP addresses, domain names, and other relevant artifacts, aid in the identification and detection of malicious activity.
Key findings include:
- In-depth examination of the infection chain used by SideCopy APT Group.
- The group uses a sophisticated and sophisticated attack methodology that starts with a phishing email and results in the installation of a Remote Access Agent (RAT) on the victim's system.
- This report aims to increase understanding and awareness of the group's tactics, techniques and procedures (TTPs) by revealing the various stages of this chain of infection.
- Organizations that understand the intricacies of SideCopy APT Group's chain of infection and the techniques they use can strengthen their security posture and develop effective risk mitigation strategies.

 Download Here
Download Here
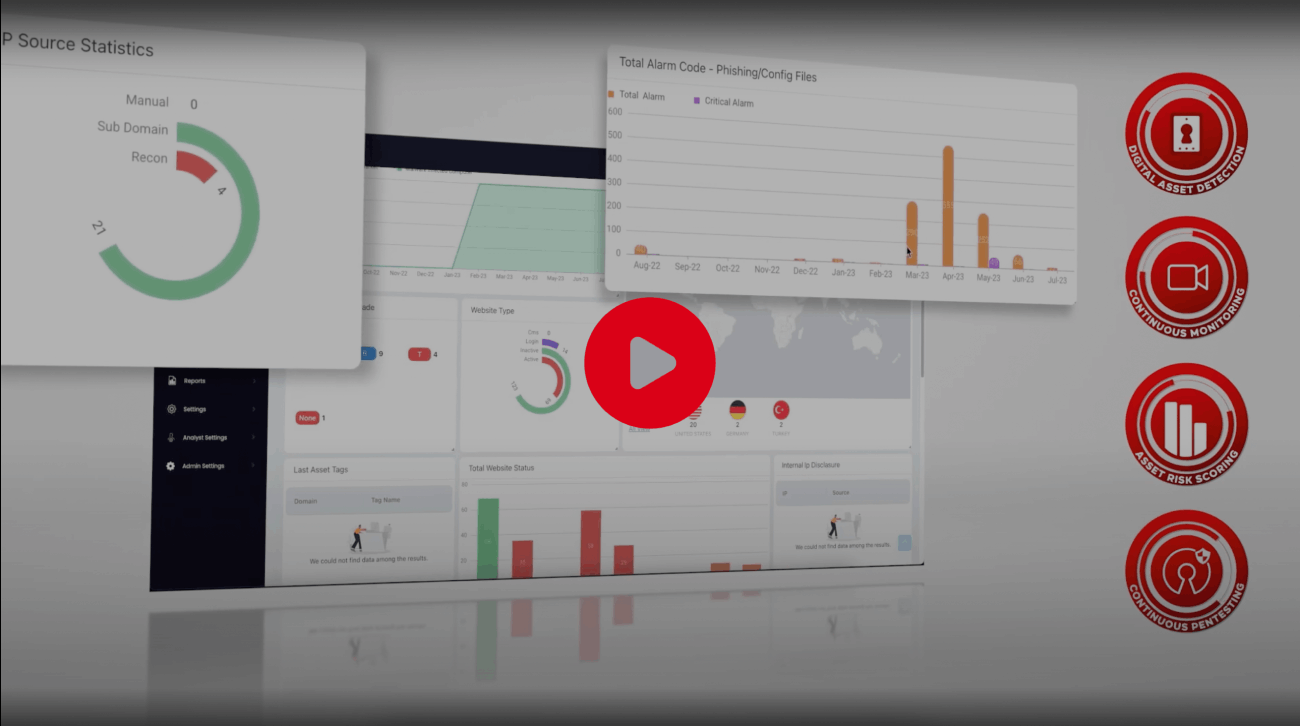
Watch the ThreatMon's Platform Intro
ThreatMon has a team of highly Threatmon's cutting-edge solution combines Threat Intelligence, External Attack Surface Intelligence, and Dark Web Intelligence to identify vulnerabilities and provide personalized security solutions for maximum security. ThreatMon identifies the distinctive nature of each business and provides bespoke solutions that cater to its specific needs.
- Identify the external assets of your business.
- Track and manage your organization's online reputation to maintain a positive image.
- Monitor social media platforms, deep/dark web activities, and rogue applications.
- Detect and mitigate digital risks such as source code leakage and account leakage.
Latest Reports
Start Your Free Trial Now!
The free trial of ThreatMon allows users to explore the product's security benefits. During this trial period, you can test Threat Intelligence data, detect threats to your organization and recommend security measures.
Start Free Trial